Azure 101 series: Protect Logic Apps Secrets with Key Vault
Tuesday, Nov 12, 2019
Key Vault
Azure Key Vault provides a centralized, secure container to protect your application secrets, which can span across your services. It allows you to store, version securely, and access the application secrets while providing granular access control policies to its secrets. Importantly, you don't need to store and manage any access keys in your application to retrieve the Key Vault secrets, and we'll see how that is possible.
Logic Apps
Logic Apps are powerful Azure workflow services that are used to easily implement business process automation and application integration through a graphical designer. But don't let the ease-of-use fool you into thinking that a quickly implemented workflow is ready for production, yet. There are few things you need to take care of before reaching a production-grade workflow, one of which is: secret management.
Usually, in these workflows, you may need to set connection strings, authentication headers, passwords, API Keys and any other secrets required for integrating with other systems. Hardcoding these secrets in the workflow must be avoided; as these will be saved as clear text in the workflow definition file, which means it is accessible to developers and Azure portal operators.
Let's see an example of how easy it is to use Key Vault secrets with Logic Apps.
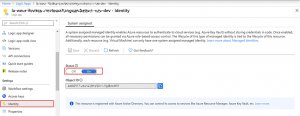
1. Assign the Logic App instance a Managed Service Identity (MSI)
First, you assign the target Logic App instance an identity in Azure Active Directory (AAD). This is an application identity that is assigned by AAD, and this is how the magic of authentication and authorization happens when the target Logic App instance access the Key Vault instance.
To assign the Logic App an MSI, you need to toggle the system assigned identity switch, as shown below.
2. Authorize the Logic App to access the Key Vault secrets
Then you need to configure the Azure Key Vault instance access policies to authorize the target Logic App instance to access its secrets during the design-time and in runtime.

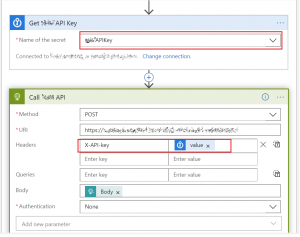
3. Access the Key Vault secret from the Logic App
Using the Logic Apps built-in [Get Secret] Action, you will be able to retrieve Key Vault secrets values in runtime securely without the need to save any keys in your application. It all happens thanks to Azure AD Managed Identity and Azure Key Vault Policies.
In the below example, I stored a backend API Key as a secret in Key Vault and used the retrieved value in the subsequent HTTP connector header.
It is worth noting that you should also consider not to track or log these secrets, and you should also obfuscate the secret values in the Logic App instance Runs History using [Secure Input/Secure Output] configuration which is available for many Logic Apps Actions and Triggers.
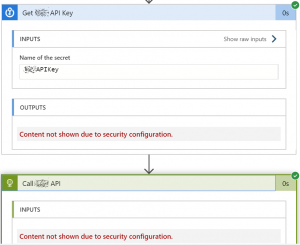
This way, your secret values in Logic Apps are still protected against unauthorized reads by Logic App developers and operators.

Comments
No comments yet
You must login to add your comment.